A MATURE FRAMEWORK
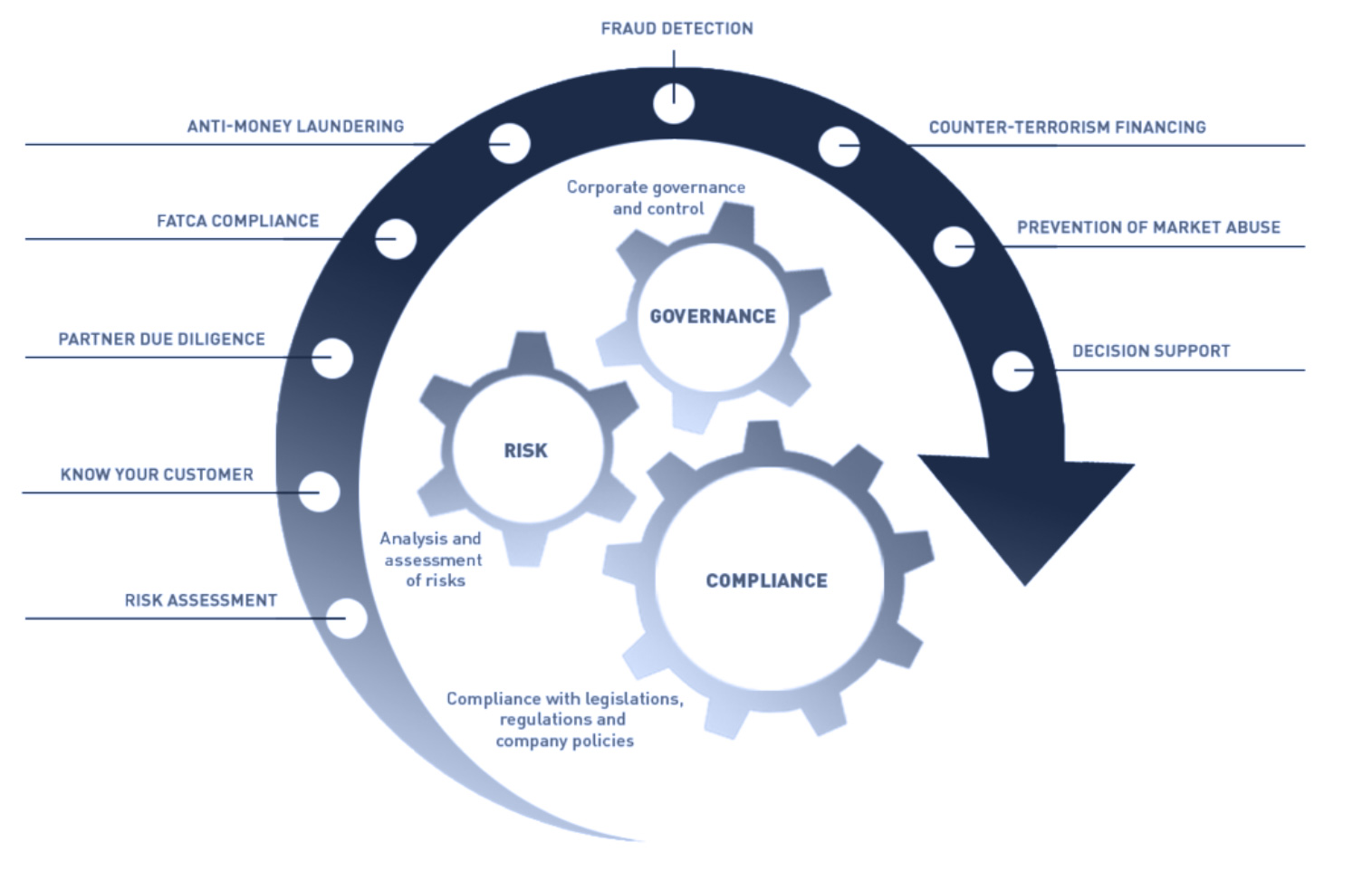
Governance Risk and Compliance (GRC) is the heart of how you will manage your security initiatives. Buying technical solutions or engaging consulting services without a plan is a sure waste of time and effort and is one of the key causes of failure with security initiatives.
QUICK SELF-EVALUATION
Quality and security of customer’s applications, solutions, and products.
Proper and mature organisation of the software development process, including control and monitoring of the development process.
Mitigation of risks of unexpected expenses for software development and support due to clear requirements and design, resulting in the reduction of production scrap and rework.
Increased security awareness and the establishment of a mature security culture of software development.
Perform Threat Modelling Exercise using STRIDE and DREAD methodologies for secure SDLC
Perform Security By Design / Security Architecture Review
Perform regular Secure Code Reviews after each Sprint
Perform Fuzz Testing
Perform Penetration Testing
Perform Cloud Security Configuration Review
Create Incident Response Plan
Execute Incident Response Plan
QUICK EVALUATION
Fort Safe offers an in-depth strategy to enable your business to maximise your security budget and initiatives while ensuring effective coverage and remediation of risks. Additionally, compliance tends to be a headache for all organizations, especially those that do not have a dedicated internal security team. Fort Safe removes the headache by managing the compliance lifecycle and giving your organisation the tools it needs to easily manage any compliance regime.
- Do you manage payment cards as well as need to be PCI-DSS Compliant?
- Are you interested in implementing the NIST Cybersecurity Framework?
- Do you have the Australian Signals Directorate Essential Eight incorporated in your company?
- Are you in need of assistance in maintaining the Australian Privacy Principles?
- Do you have customers in Europe and moreover need to ensure that you are protected for GDPR?
Fort Safe provides clients with tools and services that support our client’s integrated Governance, Risk and Compliance frameworks.
Click edit button to change this text.Fort Safe’s tools and services address the goal of automating the management of controls over critical business processes, application security and IT infrastructure security. The business goal is to improve the effectiveness of compliance oversight and to ensure compliance with laws that protect the confidentiality and integrity of critical financial, healthcare, credit card, personal information and intellectual property data.
In summary, integrated Governance, Risk and Compliance tools allow organisations to have real-time access to critical Governance, Risk and Compliance data including the performance of automated controls that monitor business processes, application security and IT infrastructure security.
An integrated Governance, Risk and Compliance framework can satisfy the following requirements:
Documentation of policies and procedures
Enforcement of policies and procedures
Continuous Monitoring of Controls to include:
Automated processes to review user access certifications and segregation of duties
Analytics dashboard for a real-time review of certification processes and risk metrics
Audit trails of actionable controls processes
Fort Safe experienced professionals can help you with Government Risk and Compliance
-
Bring your company to become ISO 27000 Compliant provide you with
-
An ISO 27000 Compliance Audit to continue your ISO 27000 Compliance
-
Also an audit for PCI-DSS Compliance
-
Advice on a roadmap to implement the NIST Cybersecurity Framework
-
An audit to verify that the ASD Essential 8 are implemented
-
Advice to make sure that you meet the Australian Privacy Principles in addition with bringing your company to become protected for the European GDPR
FORT SAFE’S PEDIGREE
If you’re ready to talk with us about your requirements, or need to unpack exactly what you should be doing, schedule a call with a Fort Safe Consultant today.
PENTESTING 101
Still need more details about Pentesting and what option may be best for your organisation?
Request a Free Consultation And Make Sure Your Business Is Protected
Book an obligation-free Vulnerability Assessment today.